Principle of Least Privilege
The Principle of Least Privilege is the only path to success.
The most important cybersecurity measure that exists is the adherence to the principle of least privilege at all layers of IT. The least privilege approach states that no person or program should have more rights in the IT systems than they need to do their jobs; access rights should be default deny as opposed to default allow. In practice, this means that nobody but the IT team should have administrator privilege access to any systems.
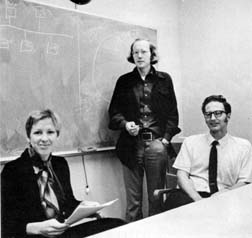
The conceptual framework for a least privilege approach to information systems was first well developed by Dr. Jerome Saltzer (seated on right in picture) at the Massachusetts Institute of Technology in the 1970’s, and was first described in his paper - Protection and the Control of Information Sharing in Multics1. Also notable is Dr. Saltzer’s tutorial publication with Michael Schroeder - The Protection of Information in Computer Systems2.
Least privilege is the most powerful information systems security measure. There isn’t a close second place. Additionally, failure to implement it properly may result in the failure of all other layers. This is because user accounts with administrator level privileges may disable or otherwise bypass other cybersecurity measures. E.g. in a Windows environment, a user account with domain administrator level privileges may be used to disable or alter logs and auditing, disable malware protection, or to embed keystroke logging software on every machine in the business.
Creating an environment of least privilege and default deny permissions is called the whitelist approach to security. Actions are disallowed by default, and allowed only when explicitly defined on a whitelist (such as a file system ACL). The inverse is called the blacklist approach to security - actions are instead default allow, and denied only when explicitly enforced by some mechanism, such as antivirus or endpoint protection software. But since no blacklist can be perfect, this approach is destined to fail. Moreover, the blacklist approach is processor and energy inefficient, as it must constantly compare the happenings in the system to the blacklist; whereas the whitelist approach places no additional load upon the system. Security and speed are both benefits to least privilege.
Microsoft produced an excellent paper on the practical application of these concepts to their Windows operating system in 2006 - Applying The Principle of Least Privilege To User Accounts On Windows XP3.
Even though these ideas were formulated decades ago, a lack of adherence to their prescriptions remains the primary cause of cybersecurity failures.
With every infrastructure build performed by Bitstream, we start from nothing and build up while never violating this principle. It’s used in configuring all systems including: workstation operating systems, server operating systems, routers, firewalls, email systems, domain registrars, DNS servers, and all other various cloud service providers.
Jerome H. Saltzer. Protection and the Control of Information Sharing in Multics. Fourth ACM Symposium on Operating System Principles, Yorktown Heights, New York, October 15-17, 1973, preprint package pages 10-24. http://web.mit.edu/Saltzer/www/publications/protmult.pdf (Original symposium version) ↩︎
Jerome H. Saltzer, and Michael D. Schroeder. The Protection of Information in Computer Systems. (invited tutorial paper) Proceedings of the IEEE 63, 9 (September 1975) pages 1278-1308. ↩︎
Anthony Steven. Applying the Principle of Least Privilege to User Accounts on Windows XP. Microsoft TechNet, Microsoft Solutions for Security and Compliance group (MSSC), January 18, 2006. http://technet.microsoft.com/en-us/library/bb456992.aspx ↩︎
Ready to get started?
Contact us to discuss how Bitstream can support your business.